CyberBay 2026 Survey Report
Insights from cybersecurity leaders on talent gaps, cost challenges, and the future of AI-driven defense.
Key Findings
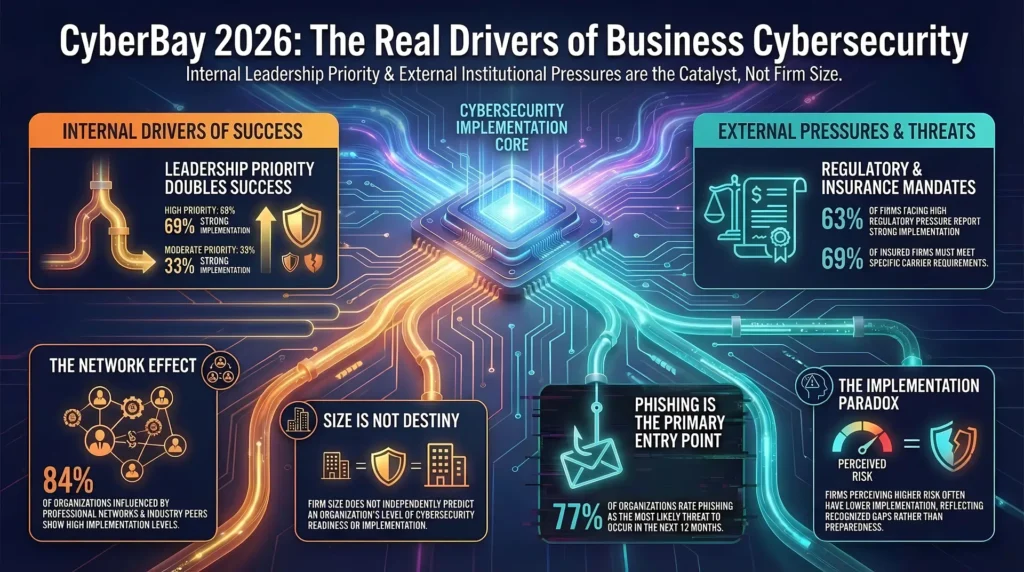
- Organizations that treat cybersecurity as a leadership priority implement stronger security practices. Among firms that report high cybersecurity priority, about 69 percent report strong implementation of cybersecurity practices, compared with about 33 percent of firms that report only moderate priority. This pattern is not random; statistical tests confirm a strong association between leadership priority and implementation.
- Professional networks and industry guidance play an important role. Organizations that report stronger influence from professional peers, consultants, industry reports, and professional associations tend to report stronger cybersecurity implementation. Among organizations reporting high levels of UNIVERSITY OF SOUTH FLORIDA / CYBER FLORIDA / BELLINI CAPITAL | 3 institutional influence, about 84 percent report high levels of cybersecurity implementation, compared with about 32 percent of organizations reporting low institutional influence. This pattern suggests that cybersecurity practices often spread through professional communities and shared industry guidance.
- Regulatory and contractual pressures also encourage cybersecurity adoption. Organizations that face stronger regulatory and external compliance pressures tend to implement stronger cybersecurity measures. Among organizations experiencing higher regulatory pressure, about 63 percent report strong implementation of cybersecurity practices, compared with about 41 percent of organizations reporting low regulatory pressure. Regulatory expectations and external compliance requirements can encourage organizations to strengthen cybersecurity practices.
- Perceived cyber risk does not always translate into stronger security practices. Organizations that perceive lower cyber risk often report stronger cybersecurity implementation. Among firms that believe cyber incidents are very unlikely, 75 percent report strong implementation of cybersecurity practices, compared with about 53 percent of firms that believe incidents are somewhat likely. This pattern suggests that organizations with stronger security practices may feel more confident in their defenses, while organizations that recognize gaps in their security posture may perceive greater exposure to cyber threats.
- Phishing is recognized as the most likely cyber incident. Across the different types of cybersecurity incidents included in the survey, phishing stands out as the one threat organizations consistently view as more likely than others. While most incident types show similar perceived likelihoods, phishing is rated as more likely to occur than ransomware, credential theft, or unauthorized access. This pattern suggests that phishing is widely recognized as the most common entry point for cyber incidents.
- Firm size alone does not determine cybersecurity readiness. Once leadership priority, institutional influences, and organizational maturity are considered, firm size does not independently predict the level of cybersecurity implementation.
Executive Summary
This report examines how small and mid-sized organizations implement cybersecurity practices and the
factors that influence their implementation. Using survey data from 202 firms, it measures perceived
cybersecurity risk, organizational priorities, cyber insurance, industry influences, and the extent of cybersecurity implementation.
The results show that organizations emphasizing cybersecurity and those influenced by professional
networks, industry guidance, and regulatory expectations report stronger cybersecurity implementation.
Regulatory and insurance requirements are also associated with greater adoption, while organizations
perceiving higher cyber risk often report lower implementation, likely reflecting recognized gaps. Notably,
firm size does not predict implementation, whereas leadership prioritization and program maturity are
more strongly associated with implementation.
The report recommends coordinated efforts: regulators, industry groups, and professional associations
should reinforce clear expectations, while internal leadership translates these into action. In short, institutional pressures and internal commitment appear to work together to improve cybersecurity outcomes.